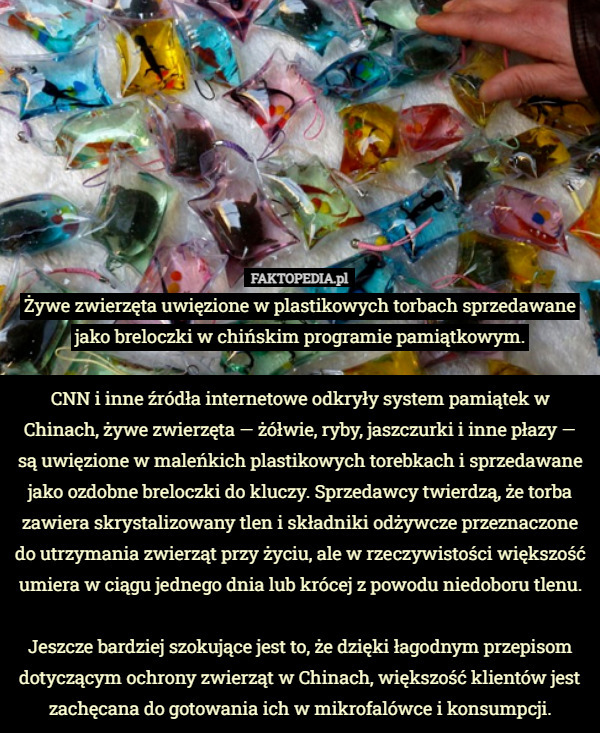
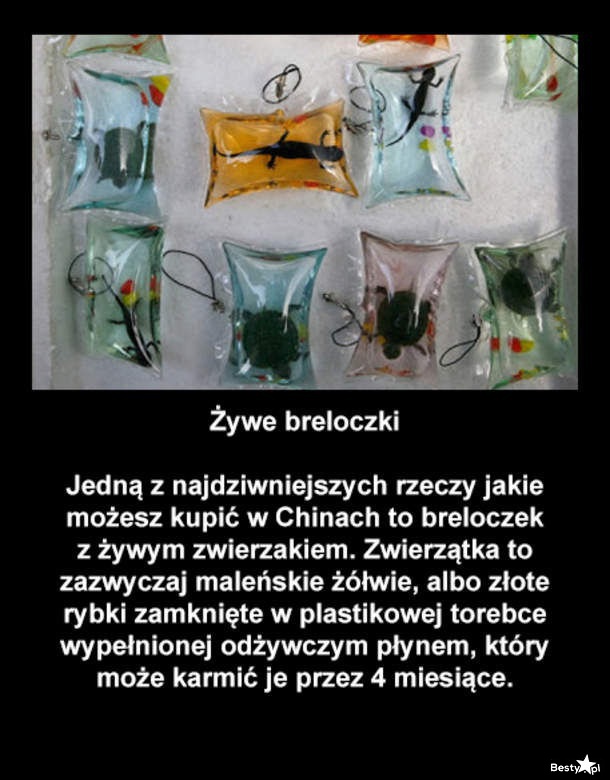
Okrutna moda w Chinach. Breloczki z żywymi zwierzętami w środku [WIDEO... (najnowsze komentarze) :: Wykop.pl

Zapomnij o tych atrakcjach turystycznych. Choć wyglądają niewinnie, stoi za nimi krzywda. 10 nieetycznych rozrywek | Dziennik Polski

Najbardziej okrutne pamiątki z wakacji. Jeśli masz choć odrobinę współczucia, nie kupuj - WP Turystyka

Najbardziej okrutne pamiątki z wakacji. Jeśli masz choć odrobinę współczucia, nie kupuj - WP Turystyka



















![Okrutna moda w Chinach. Breloczki z żywymi zwierzętami w środku [WIDEO] | Wiadomości Radio ZET Okrutna moda w Chinach. Breloczki z żywymi zwierzętami w środku [WIDEO] | Wiadomości Radio ZET](https://gfx.wiadomosci.radiozet.pl/var/radiozet-wiadomosci/storage/images/blisko-ludzi/okrutna-moda-w-chinach-breloczki-z-zywymi-zwierzetami-w-srodku-wideo/112266-1-pol-PL/Okrutna-moda-w-Chinach.-Breloczki-z-zywymi-zwierzetami-w-srodku-WIDEO_article.jpg)