Basket League: Την 8η αγωνιστική το «αιώνιο» ντέρμπι στο ΣΕΦ - Όλο το πρόγραμμα (ΦΩΤΟ) | Filathlos.gr | Το Εγκυρότερο Αθλητικό Blog!

Παναθηναϊκός-Ολυμπιακός: Δείτε τα καλύτερα "κλικ" από την μεγάλη πρόκριση του "τριφυλλιού" στο μπάσκετ (pics) - ΠΑΟ ΠΑΝΤΟΥ - Νέα & Ειδήσεις για τον Παναθηναϊκό

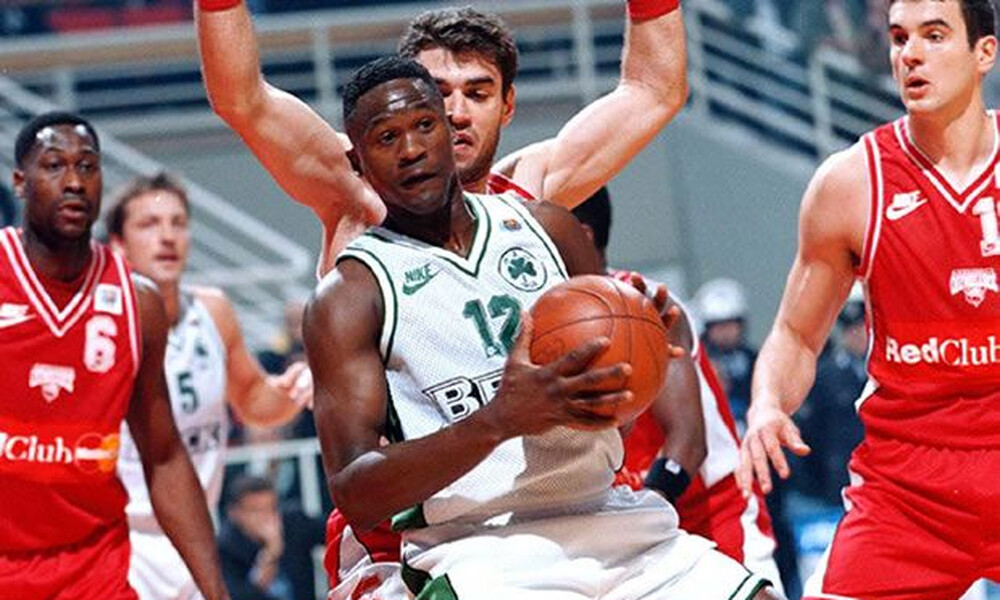
The Basketbook - Είναι μερικές φωτογραφίες που εκτός από εικόνα, έχουν και πολύ ήχο μέσα τους. Με δυνατούς ήχους μας μεταφέρουν το ένδοξο παρελθόν, αλλά ανά διαστήματα ακούμε και ψιθύρους. Τους ψιθύρους

Ο Παναθηναϊκός «ξύπνησε» στο δεύτερο ημίχρονο και νίκησε τον ΠΑΟΚ | Filathlos.gr | Το Εγκυρότερο Αθλητικό Blog!

H ΦΩΤΟΓΡΑΦΗΣΗ ΤΗΣ OMAΔΑΣ ΕΦΗΒΩΝ ΤΗΣ ΑΚΑΔΗΜΙΑΣ ΜΠΑΣΚΕΤ ΤΟΥ ΠΑΝΙΩΝΙΟΥ 2019-2020 1. ΓΚΙΚΑΣ ΝΙΚΟΣ 4. ΜΑΝΤΕΛΑΣ ΓΙΑΝΝΗΣ 5. ΝΟΥΡΤΣΕΛΛΑΡΙ ΑΛΕΞΑΝΔΡΟΣ 6. ΚΟΥΤΣΟΥΜΑΡΗΣ ΧΡΥΣΑΝΘΟΣ 7. ΚΑΝΕΛΛΟΠΟΥΛΟΣ ΓΙΩΡΓΟΣ 8. ΣΚΑΡΜΟΥΤΣΟΣ ΣΠΥΡΟΣ 9. ΚΩΣΤΑΚΟΠΟΥΛΟΣ ΔΗΜΗΤΡΗΣ
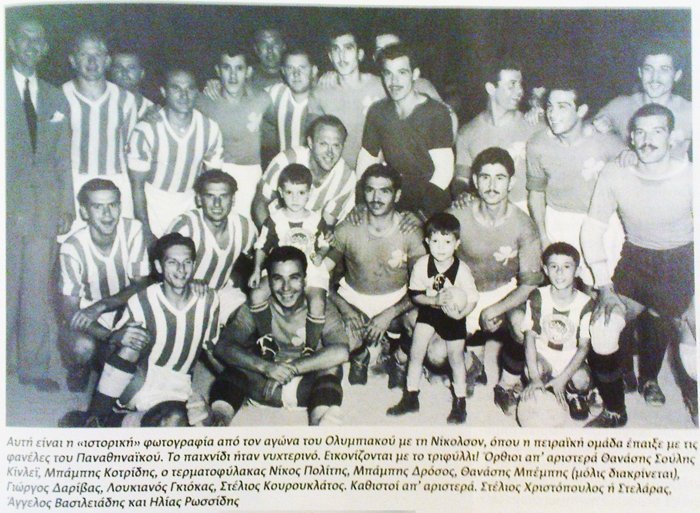
BNSports.gr - Ολυμπιακός με τριφύλλι στο στήθος! Η μέρα που οι ερυθρόλευκοι φόρεσαν στολή του Παναθηναϊκού για ένα ματς!