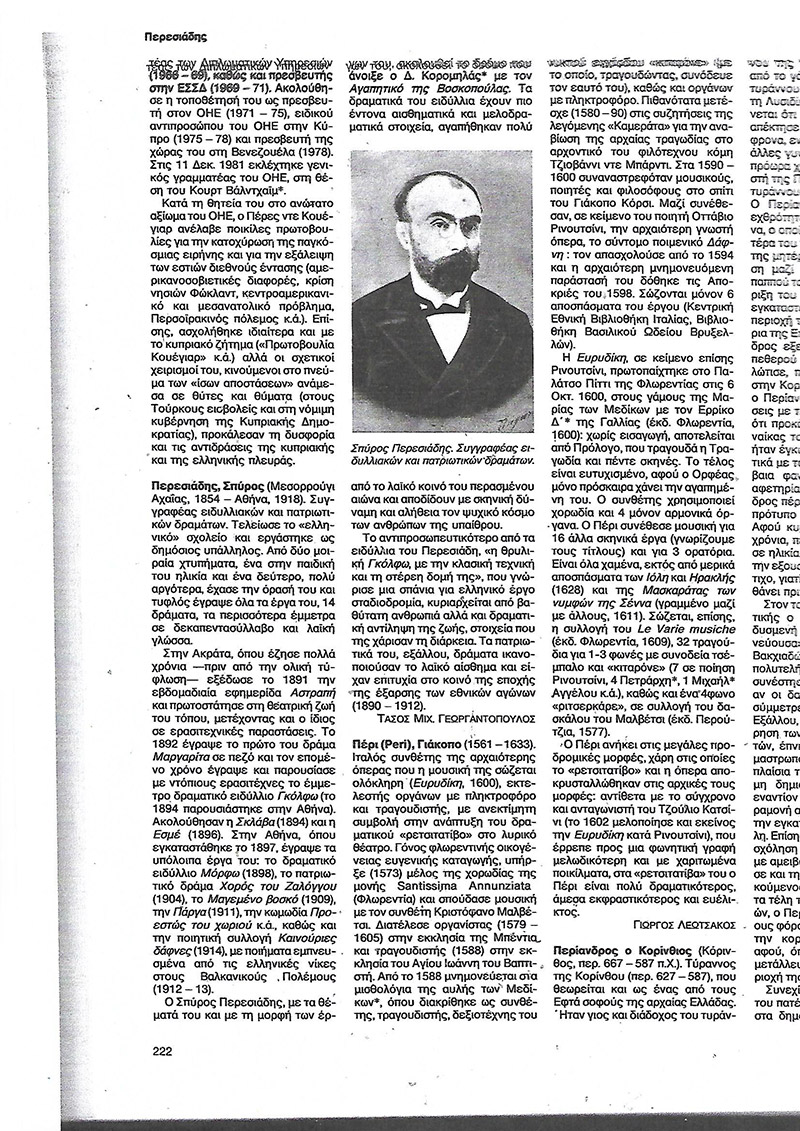
Τανταλίδης: Ο Φαναριώτης ποιητής - Περεσιάδης: Τα απίστευτα ατυχήματα που τύφλωσαν τον συγγραφέα της «Γκόλφως»
Τανταλίδης: Ο Φαναριώτης ποιητής - Περεσιάδης: Τα απίστευτα ατυχήματα που τύφλωσαν τον συγγραφέα της «Γκόλφως»

PDF) Η Γκόλφω του Περεσιάδη και οι σκηνικές αναζητήσεις του Σίμου Κακάλα και του Νίκου Καραθάνου. Φύση, φως και σκότος. | Tania (Stamatia) Neofytou - Academia.edu

O Τανταλίδης κι ο Φαναριώτης ποιητής Περεσιάδης... Τα απίστευτα ατυχήματα που τύφλωσαν τον συγγραφέα της «Γκόλφως» - Eurohoops






















